A company or organization that wants to provide services that rely on identities provided by SWAMID members does not usually need to become a member of SWAMID. For the SAML WebSSO technology profile the service provider only has to accept the SWAMID Metadata Terms of Use (ToU). This acceptance does not have to be communicated to SWAMID.
NOTE WELL
Requesting registration of a service provider in SWAMID implies acceptance of the SWAMID Metadata Terms of Use (ToU).
SWAMID WebSSO Service Provider
How to provide services to users associated with SWAMID members
Is your service provider already published to the interfederation eduGAIN by another federation?
We have an opt-out policy regarding eduGAIN for SWAMID Identity Providers, so you should already been able to communicate with most SWAMID member institutions. You may need to talk to the federation that publishes your metadata to eduGAIN about which eduGAIN enabled entity categories to use to get the appropriate attributes released by our IdPs.
If you still want to register your service with SWAMID:
Review and decide to accept the SWAMID Metadata Terms of Use (ToU). If you accept the ToU you do not need to communicate this to SWAMID Operations.
- We tag Service Providers with entity categories and encourage our IdPs to use them for attribute release. Please read through our Entity Categories for Service Providers and decide which apply best for you. Please provide a motivation for your choice as described in the defined request processes for each entity category! SWAMID has a defined Attribute Profile that describes the normal use of attributes within the federation.
- Email SWAMID Operations to register and publish metadata for the service provider. This step implies acceptance of the ToU and constitutes a legally binding agreement to abide by the ToU. Please look into step 4 in the Shibboleth Service Provider installation instructions below to make your service provider work better with users within the federation and inter-federations.
- Integrate SWAMID Metadata into the service provider and optionally configure use of the SWAMID Discovery Service.
How to install a Shibboleth Service Provider
Step 1 - Installing a Web Server
- Installing Apache Web Server 2.0 or higher with Shibboleth Service Provider
- Configuring Apache Web Server to use Shibboleth
- Installing IIS for MS windows 7.0 or higher
- Configuring IIS for MS windows
- Docker Image with apache and shibboleth
Step 2 - Installing Shibboleth Service Provider
- Installera Shibboleth SP - Linux med PKG
- Installera Shibboleth SP - Linux med RPM
- Installera Shibboleth SP - Windows med webbservern IIS
- Shibboleth for Java Applications
Step 3 - Configuring Shibboleth Service Provider for use in the SWAMID federation
- Configure Shibboleth SP - shibboleth2.xml
- Configure Shibboleth SP - attribute-map.xml
- Configure Shibboleth SP - Check for Identity Assurance
- How to inform user of missing required attributes when accessing a service
Step 4 - Get your Service Provider's metadata into the SWAMID Metadata stream
When you got your web service ready with a installed and running Service Provider you need to make it easier for the users to use your service. The hardest step is to make the identity providers to release needed attributes to your service. This can be done in two different ways and you need to do both of them.
- Enable support for automatic attribute release from identity providers with Entity Categories for Service Providers.
- If your service shall be available within the international academic identity federations inform SWAMID Operations that your Service Provider shall be exported to eduGAIN.
- Contact the identity providers that you've know that you have users from and be sure that they release needed attributes, preferable with an entity category and with a manual release if you need special attributes, ie. entitlements.
Don't forget to enhance user experience with Service Provider Metadata Extensions for Login and Discovery User Interface (MDUI). Look at the example to understand what the MDUI information can do with the user experience. More information and good practice for how to design a good login user interface can be found in the REFEDS login and discovery guidelines.
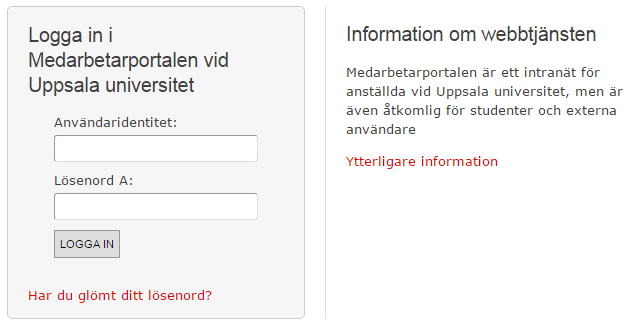
Example of MDUI use in an Identity Provider. The text (title and description) on the right is provided by Service Provide MDUI elements in SWAMID metadata for the service "Medarbetarportalen".